
Ransomware –
The most serious threat right now
More and more criminals are gaining access to networks, spying on them and encrypting data – then suddenly nothing works anymore – or they threaten to publish sensitive data unless a ransom is paid.
Ransomware can cost countless euro, trust and customers
The most serious threat to your corporate network will come from ransomware campaigns, whose methods and resources are becoming increasingly similar to state-sponsored APTs (Advanced Persistent Threat) and large-scale penetration tests – according to the German Federal Office for Information Security (BSI). Infected systems are analyzed, and victims are blackmailed with the encryption of data or threats of publication. The consequences are serious: they range from short-term work and production restrictions to complete breakdowns lasting months. However, it is not only loss of sales, system recovery costs, and often ransom payments in the millions that impact businesses, but also a loss of trust on the part of customers.
Criminals use deceit to exploit security vulnerabilities
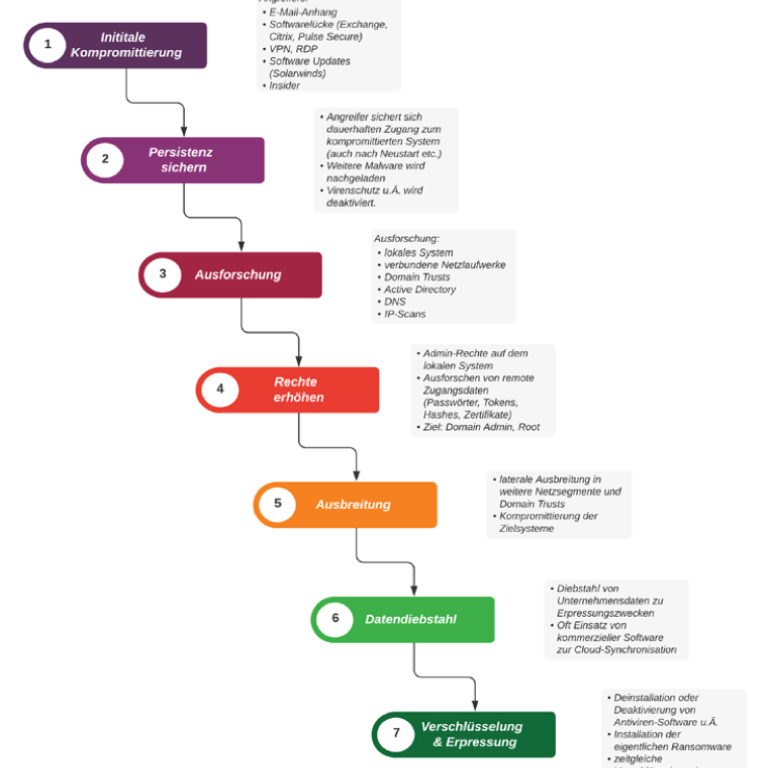
Access to networks
Alongside phishing and email attachments, security vulnerabilities in the products of major manufacturers (Microsoft Exchange, Citrix Netscaler, Pulse Secure VPN), compromised updates (Solarwinds) and unsecured RDP and VPN access play a major role.
Shared work, shared tools
Cybercriminals are increasingly collaborating with one another. Individual attack stages are carried out by different actors who share tools and platforms. Large ransomware groups use affiliate models or also make their services available to third parties in the form of Ransomware-as-a-Service. Excellent profit potential is an additional motivator, leading to more and more widespread attacks.
Implement an effective intrusion detection system quickly – with zero impact on your existing IT and OT systems.
Analysis of current ransomware variants
 cybersense:~ unsuspicious$ ls
cybersense:~ unsuspicious$ lsREvil / Sodinokibi
DoppelPaymer
Egregor
Clop
Darkside
Defray777
IEncrypt / BitPaymer
Nefilim
In 40 pages, learn about the latest techniques and tools used by attackers and how Cybersense Deception counters – and disables – them at different stages of the cyber kill chain.

Do you have any questions? Would you like a demo?
We look forward to hearing from you.
Your contact partner
Michael Pütz